Cybercriminals Exploit Free Software Lures to Deploy Hijack Loader and Vidar Stealer


Meta announced it is delaying the training of its large language models (LLMs) using public content shared by adults on Facebook and Instagram following the Irish Data Protection Commission (DPC) request.
“The DPC welcomes the decision by Meta to pause its plans to train its large language model using public content shared by adults on Facebook and Instagram across the EU/EEA. This decision followed intensive engagement between the DPC and Meta.” reads the DPC’s request. “The DPC, in co-operation with its fellow EU data protection authorities, will continue to engage with Meta on this issue.”
Meta added it is disappointed by request from the Irish Data Protection Commission (DPC), the social network giant pointed out that this is a step “backwards for European innovation, competition in AI development and further delays bringing the benefits of AI to people in Europe.”
“We’re disappointed by the request from the Irish Data Protection Commission (DPC), our lead regulator, on behalf of the European DPAs, to delay training our large language models (LLMs) using public content shared by adults on Facebook and Instagram — particularly since we incorporated regulatory feedback and the European DPAs have been informed since March.” reads the statement from Meta. “This is a step backwards for European innovation, competition in AI development and further delays bringing the benefits of AI to people in Europe.”
The company explained that its AI, including Llama LLM, is already available in other parts of the world. Meta explained that to provide a better service to its European communities, it needs to train the models on relevant information that reflects the diverse languages, geography and cultural references of the people in Europe. For this reason, the company initially planned to train its large language models using the content that its European users in the EU have publicly stated on its products and services.
Meta intended to implement these changes on June 26, giving users the option to opt out of data usage by submitting a request.
“
“We are committed to bringing Meta AI, along with the models that power it, to more people around the world, including in Europe. But, put simply, without including local information we’d only be able to offer people a second-rate experience. This means we aren’t able to launch Meta AI in Europe at the moment.”
Meta added that the delay will allow it to address requests from the U.K. Information Commissioner’s Office (ICO) before starting the training.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Meta)


Keytronic has confirmed a data breach after a ransomware group leaked allegedly stolen personal information from its systems. The company did not provide any info on the ransomware operation that hit its network, however Black Basta ransomware group leaked over 500 gigabytes of data allegedly stolen from the company. Black Basta ransomware group claims to have stolen ≈530 GB of data, including HR, Finance, Engineering documents, Corporate data, and home users data.

The company was forced to halt domestic and Mexico operations for approximately two weeks.
“The cybersecurity incident caused disruptions, and limitation of access, to portions of the Company’s business applications supporting aspects of the Company’s operations and corporate functions, including financial and operating reporting systems.” reads the FORM 8-K/A filed with SEC. “Since the date of the Original Report, the Company has determined that the threat actor accessed and exfiltrated limited data from the Company’s environment, which includes some personally identifiable information.”
As of the date of the FORM 8-K filing, the company has restored its operations and corporate functions and locked out the unauthorized third party.
Keytronic is notifying potentially affected parties and regulatory agencies.
The company confirmed that it has already incurred $600,000 in expenses related to the cybersecurity incident to date. The bad news is that financial losses are greater due to lost production for approximately two weeks in its domestic and Mexico operations.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Keytronic)


Initially, these attacks involved malicious software that encrypts a victim’s data, rendering it inaccessible until a ransom is paid to the attackers.
Today, this tactic has evolved, where ransomware operators in nearly every case first exfiltrate sensitive data and then threaten to publicly expose it if a ransom demand is not paid.
In some cases, attackers are even leveraging the threat of regulatory actions or causing cyber insurance policies to be rendered moot by reporting lapses in security on the part of the victim to regulators and insurers.
In other cases, they may initiate a Denial of Service (DoS) attack to damage the victim’s public image or try to extort third parties like customers or business partners impacted by the data breach. These tactics are used individually or in unison to increase pressure to twist the victim organization’s arm into paying up.
In all cases, the economic impact from ransomware is profound, affecting businesses, governments, and individuals globally. Understanding the economic factors driving ransomware is crucial for developing effective strategies to fight this growing scourge.
RaaS: Mirroring the Legitimate SaaS Models
In mid-2012, the ransomware ecosystem evolved with the introduction of Reveton, the first Ransomware-as-a-Service (RaaS). This revolutionized the cybercrime landscape, making it easier for people with minimal technical skills to commit ransomware attacks. The RaaS model mirrors the legitimate Software-as-a-Service (SaaS) model, where developers create and maintain the tools and lease them to affiliates in exchange for a share of the profits.
The RaaS ecosystem is made up of specialists like developers, affiliates, access brokers and more, each playing a role. Developers author sophisticated ransomware variants and provide regular updates to ensure their efficacy. Affiliates are the actors who distribute the ransomware through phishing emails, exploit kits, or compromised websites, while access brokers sell access to compromised networks. The top-down hierarchical structures, diversified revenue streams, and businesses functions including customer support have transformed RaaS into highly profitable “organizations.”
The Dark Web is a bustling, underground marketplace for malefactors, where ransomware kits, stolen data, and support services are bought and sold. These marketplaces offer a wide range of tools and services, including customer support for cybercriminals, ensuring that even attackers who are green behind the ears can perpetrate successful ransomware campaigns.
Cybercriminal gangs often operate across borders, leveraging a global network to slip through the nets of law enforcement. They use all possible tools, including compromised servers and anonymizing services, for obfuscation, making it hard for authorities to trace and shut down their operations.
Unfortunately Crime Does Pay
Ransomware attacks are widespread because they promise a maximum reward for minimum effort. Ransom demands range from thousands to millions of dollars, and unfortunately, many victims cough up to regain access to their data and systems quickly. High-profile cases, such as the Colonial Pipeline attack, have seen ransom payments in the multimillion-dollar range.
Carrying out a ransomware attack takes minimal initial investment, particularly when using the RaaS model. Affiliates can start with no upfront cost, paying developers a percentage of the ransom payments they collect. This low barrier to entry adds to the proliferation of these attacks.
Moreover, the ROI for ransomware gangs is exceptionally high. The potential payouts from successful attacks dwarf the costs of developing or renting ransomware. This ROI makes ransomware a compelling business model for criminals, so it is soaring in popularity.
The Digital Currency of Crime
Cryptocurrencies play a central role in ransomware economics by offering anonymity and privacy that traditional payment methods cannot match. Bad actors usually demand payment in cryptocurrencies such as Bitcoin or Monero, which are difficult to trace and keep their identities anonymous.
Transactions with crypto are fast and easy, facilitating rapid payment and verification. This speed and simplicity are great for attackers who want to get their hands on the ransom immediately and for victims who wish to restore their operations as soon as possible.
Furthermore, law enforcement faces significant hurdles in tracking and seizing cryptocurrency used for nefarious purposes. The decentralized nature of cryptocurrencies and the use of anonymizing techniques make it extremely difficult to trace transactions and recover money.
While there have been some successful recovery efforts, such as seizing a portion of the Colonial Pipeline ransom, the money is gone for good in most instances.
Counting the Cost for Companies
Entities hit by ransomware attacks have to pay direct costs, including ransoms and expenses related to recovery and remediation. Even if the ransom is not paid, the costs associated with restoring data from backups and strengthening security can be substantial.
The indirect costs of ransomware attacks are often even more damaging. Downtime and lost productivity during the event and recovery period can severely impact business operations. Additionally, reputational damage and loss of customer trust are immeasurable and have long-term financial consequences that impact the company’s bottom line. In fact, the cost to victims from ransomware attacks is estimated to reach $265 billion (USD) annually by 2031.
The increased frequency and volume of attacks has also seen cybersecurity insurance premiums soar and spending on cybersecurity measures skyrocket. Businesses are investing more in employee training, advanced security tools, and incident response planning to mitigate the risk of future attacks.
Limiting the Financial Fallout
Proactive cybersecurity measures are essential for defending against ransomware. Implementing endpoint and anti-ransomware protection, patch management, and access controls can dramatically reduce the risk of a successful attack. Defenses like data backups can help you limit the impact of ransomware, while resilience and procedure testing can help you effectively recover from an attack and reduce operational disruptions. Finally, employee training and awareness programs are vital in preventing ransomware attacks.
On the other hand, cybersecurity frameworks governing cryptocurrencies and fostering international cooperation are crucial for combating ransomware. Better Anti-Money Laundering (AML) and Know-Your-Customer (KYC) regulations can help reduce the anonymity of cryptocurrency transactions, while international collaboration can help catch and prosecute these gangs across borders.
A Complex and Evolving Threat
Ransomware is a complex and evolving threat that isn’t going anywhere soon – it’s simply too profitable for threat actors. However, understanding the tactics of the top ransomware groups and the economic dynamics behind this menace can help businesses develop more effective strategies to fight it.
A multi-pronged approach, including strengthening cyber defenses, improving regulations, and raising awareness, is crucial to mitigating the risk and impact of ransomware.
About the author
Kirsten Doyle has been in the technology journalism and editing space for nearly 24 years, during which time she has developed a great love for all aspects of technology, as well as words themselves. Her experience spans B2B tech, with a lot of focus on cybersecurity, cloud, enterprise, digital transformation, and data centre. Her specialties are in news, thought leadership, features, white papers, and PR writing, and she is an experienced editor for both print and online publications. She is also a regular writer at Bora.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, cybercrime)
Last Week in Security is a summary of the interesting cybersecurity news, techniques, tools and exploits from the past week. This post covers 2024-06-10 to 2024-06-17.
This section is for news, techniques, write-ups, tools, and off-topic items that weren't released last week but are new to me. Perhaps you missed them too!
Techniques, tools, and exploits linked in this post are not reviewed for quality or safety. Do your own research and testing.
Two men, Thomas Pavey (aka “Dopenugget”) and Raheim Hamilton (aka “Sydney” and “Zero Angel”), have been charged in federal court in Chicago for operating the dark web marketplace “Empire Market” from 2018 to 2020.
According to the indictment, the duo was previously involved in selling counterfeit U.S. currency on AlphaBay before starting Empire Market.
The two men are accused of having facilitated over four million transactions for a total value of more than $430 million, involving illegal goods and services. The authorities charged them with various crimes, including drug trafficking, computer fraud, access device fraud, counterfeiting, and money laundering, which carry a maximum sentence of life in federal prison. Pavey and Hamilton are currently in U.S. law enforcement custody, with arraignments yet to be scheduled.
“THOMAS PAVEY, also known as “Dopenugget,” 38, of Ormond Beach, Fla., and RAHEIM HAMILTON, also known as “Sydney” and “Zero Angel,” 28, of Suffolk, Va., owned and operated Empire Market from 2018 to 2020, during which time they facilitated approximately four million transactions between vendors and buyers valued at more than $430 million, according to a superseding indictment returned Thursday in U.S. District Court in Chicago.” reads the press release published by DoJ. “They began operating Empire Market on Feb. 1, 2018, the indictment states.”
The dark web marketplace Empire Market featured multiple categories of illicit goods such as illegal drugs, counterfeit items, Software & Malware, and credit card numbers, it allowed its users to pay using Bitcoin (BTC), Monero (XMR), and Litecoin (LTC).
The dark web marketplace shut down in 2020, leaving users without time to withdraw funds from their escrow accounts, at the time some users blamed a prolonged denial-of-service (DDoS) attack, while others suspected an exit scam.
The two operators used cryptocurrency to conceal the nature and identities involved in the illicit transactions and encouraged users to use “tumbling” services, which mix and exchange cryptocurrencies to obscure their origin and connection to the marketplace.
During the investigation, the feds seized $75 million worth of cryptocurrency at the time of the seizures, as well as cash and precious metals.
Pavey and Hamilton face charges for five counts:
The two men can face a maximum sentence of life in federal prison.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Empire Market)
In late 2023, Sygnia researchers responded to an incident suffered by a large organization that they attributed to a China-linked threat actor tracked as ‘Velvet Ant.’
The cyberspies deployed custom malware on F5 BIG-IP appliances to gain persistent access to the internal network of the target organization and steal sensitive data.
The investigation revealed that the threat actor had been present in the organization’s on-premises network for about three years, aiming to maintain access for espionage purposes. They achieved persistence by establishing multiple footholds within the company’s environment. One method used was exploiting a legacy F5 BIG-IP appliance exposed to the internet, which served as an internal Command and Control (C&C). When one foothold was discovered and remediated, the threat actor quickly adapted and pivoted to another. This demonstrated their agility and deep understanding of the target’s network infrastructure.
The investigation revealed that the Chinese hackers had been present in the organization’s on-premises network for about three years. They achieved persistence by establishing multiple footholds within the company’s environment. One method used was exploiting a legacy internet-facing F5 BIG-IP appliance, which was also used by attackers as an internal Command and Control (C&C). After the researchers discovered and remediated one foothold, the APT group quickly pivoted to another. This demonstrated their agility and deep understanding of the target’s network infrastructure.
“The compromised organization had two F5 BIG-IP appliances which provided services such as firewall, WAF, load balancing and local traffic management. These appliances were directly exposed to the internet, and both of which were compromised. Both F5 appliances were running an outdated, vulnerable, operating system. The threat actor may have leveraged one of the vulnerabilities to gain remote access to the appliances.” reads the analysis published by Sygnia. “As a result, a backdoor hidden within the F5 appliance can evade detection from traditional log monitoring solutions.”
Once the attackers had compromised the F5 BIG-IP appliances, they gained access to internal file servers and deployed the PlugX RAT. The PlugX RAT was used by multiple Chinese APT groups in cyberespionage campaigns over the years.
Forensic analysis of the F5 appliances revealed that the Velvet Ant group also used the following malware in their attacks:
Forensic analysis of the F5 appliances identified four binaries deployed by the threat actor:

Researchers provided the following recommendations for organizations to mitigate attacks of groups like Velvet Ant:
The report also includes indicators of compromise for the attack analyzed by the researchers.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Velvet ANT APT)

The LA County’s Department of Public Health announced that the personal information of more than 200,000 was compromised after a data breach that occurred between February 19 and February 20, 2024.
Threat actors obtained the log-in credentials of 53 Public Health employees through a phishing campaign.
“Between February 19, 2024, and February 20, 2024, the Los Angeles County Department of Public Health experienced a phishing attack in which a hacker was able to gain log-in credentials of 53 Public Health employees through a phishing email, compromising the personal information of more than 200,000 individuals.” reads the notice of data breach published by DPH.
Upon discovering the phishing attack, Public Health disabled the impacted email accounts, and reset and reimaged the user’s device. The organization also blocked websites that was the origin of the attack and quarantined all suspicious incoming emails.
Potentially compromised e-mail accounts may have included DPH clients/employees/other individuals’ first and last name, date of birth, diagnosis, prescription, medical record number/patient ID, Medicare/Med-Cal number, health insurance information, Social Security Number, and other financial information.
“Affected individuals may have been impacted differently and not all of the elements listed were present for each individual.” continues the notice.
LA County’s Department of Public Health is notifying impacted individuals by mail.
The company is informing the U.S. Department of Health & Human Services’ Office for Civil Rights and other relevant agencies.
In response, Public Health has implemented numerous enhancements to reduce exposure to similar e-mail attacks in the future.
At the time of this writing, DPH cannot confirm if any information has been accessed or misused. The company recommends that impacted individuals review the content and accuracy of their medical records with their medical providers.
DPH announced it has implemented several enhancements to reduce exposure to similar email attacks in the future.
The agency is also offering entitled individuals free credit and identity monitoring services.
In April, the Los Angeles County Department of Health Services disclosed a data breach that impacted thousands of patients. Patients’ personal and health information was exposed after a phishing attack impacted over two dozen employees.
Los Angeles County Department of Health Services operates the public hospitals and clinics in Los Angeles County, and is the United States’ second largest municipal health system, after NYC Health + Hospitals.
The phishing attack occurred between February 19, 2024, and February 20, 2024. Attackers obtained the credentials of 23 DHS employees.
“A phishing e-mail tries to trick recipients into giving up important information. In this case, the DHS employees clicked on the link located in the body of the e-mail, thinking that they were accessing a legitimate message from a trustworthy sender.” reads the data breach notification sent to the impacted individuals. “Due to the ongoing investigation by law enforcement, we were advised to delay notifying you of this incident until now, as public notice may have hindered their investigation.”
The compromised information varied for each individual, potentially exposed information included the patient’s first and last name, date of birth, home address, phone number(s), e-mail address, medical record number, client identification number, dates of service, and/or medical information (e.g., diagnosis/condition, treatment, test results, medications), and/or health plan information.
Social Security Numbers (SSN) or financial information was not compromised.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, LA County’s Department of Public Health)


Spanish police arrested a 22-year-old British national who is suspected of being a key member of the cybercrime group known as Scattered Spider (also known as UNC3944, 0ktapus). The man was arrested in Palma de Mallorca while attempting to fly to Italy, during the arrest, police confiscated a laptop and a mobile phone. The arrest resulted from a joint operation conducted by the U.S. Federal Bureau of Investigation (FBI) and the Spanish Police.
“A 22-year-old British man has been arrested in Palma de Mallorca in a joint effort by Spanish police and the FBI on suspicion of being the ringleader of a hacking group which targeted 45 companies and people in the United States.” reported the Murcia Today. “He stands accused of hacking into corporate accounts and stealing critical information, which allegedly enabled the group to access multi-million-dollar funds.”
The cybercrime group Scattered Spider is suspected of hacking into hundreds of organizations over the past two years, including Twilio, LastPass, DoorDash, and Mailchimp.
While Murcia Today did not provide info about the arrested man, vx-underground states that the individual was involved in “several other high-profile ransomware attacks performed by Scattered Spider.”
vx-underground also added that the man arrested is a SIM-swapper known by the alias “Tyler.”
June 14th a 22-year-old British man was arrested in Palma de Mallorca, Spain.
— vx-underground (@vxunderground) June 15, 2024
Per the official report: the currently unidentified male is alleged to be behind a series of large-enterprise 'hacks' which resulted in the theft of corporate information and allowing an unidentified… pic.twitter.com/jygRdfCUpu
Previously on Dragon Ball Z, the Spanish media reported a 'hacker' was arrested via the Spanish Police working in conjunction with the United States Federal Bureau of Investigation.
— vx-underground (@vxunderground) June 15, 2024
The individual arrested as a 22-year-old male from the United Kingdom. He was not immediately…
According to the Spanish police, the man once controlled Bitcoins worth $27 million. According to the malware research team, a judge in Los Angeles, California, has issued a warrant for the arrest of the British citizen. Spanish police tracked the suspect to Mallorca after he entered Spain via Barcelona in late May. The investigation is still ongoing. The police have yet to disclose the suspect’s identity.
The popular journalist Briand Krebs reported that sources familiar with the investigation told KrebsOnSecurity the man is a 22-year-old from Dundee, Scotland named Tyler Buchanan.
“Sources familiar with the investigation told KrebsOnSecurity the accused is a 22-year-old from Dundee, Scotland named Tyler Buchanan, also allegedly known as “tylerb” on Telegram chat channels centered around SIM-swapping.” states KrebsOnSecurity.
In January 2024, U.S. authorities arrested Noah Michael Urban, a 19-year-old from Palm Coast, Florida, suspected of being a member of the Scattered Spider cybercriminal group. He is accused of stealing at least $800,000 from five victims between August 2022 and March 2023. Urban, known online as “Sosa” and “King Bob,” is linked to the same group that hacked Twilio and other companies in 2022.
Scattered Spider members are part of a broader cybercriminal community called “The Com,” where hackers brag about high-profile cyber thefts, typically initiated through social engineering tactics like phone, email, or SMS scams to gain access to corporate networks.
“One of the more popular SIM-swapping channels on Telegram maintains a frequently updated leaderboard of the most accomplished SIM-swappers, indexed by their supposed conquests in stealing cryptocurrency. That leaderboard currently lists Sosa as #24 (out of 100), and Tylerb at #65.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Scattered Spider)
Often, behind these enticing offers are pyramid schemes in which profits are generated through the recruitment of new participants, rather than through actual service, sometimes even causing significant financial losses. Other false offers may require initial investment without ever seeing a significant return or promise job opportunities with hidden fees. t is into this scenario that illicit practices such as moneny mules and reshipping scams can fit.
Money mules
This practice is illegal and encourages money laundering and other criminal activities. The term money mules refers to those individuals who are recruited by criminals to transfer illicit money through their bank accounts in exchange for a commission. Money mules are often unaware that they are committing a crime and think they are doing regular work.
In this regard, the State Police’s latest operation “EMMA 9,” a vast action to combat cyber money laundering coordinated by Europol and conducted in 28 countries, uncovered 2,729 fraudulent transactions, identified 879 money mules and foiled fraud worth more than 6 million euros.
“The phenomenon of money mules certainly represents one of the established and ever-present aspects of online fraud. These individuals constitute the last link in the chain through which criminals monetize the proceeds of crime.” comments the State Police, “In the context of countering FinancialCybercrime, the prevalence of these figures is alarming and is endemic worldwide.”
“Drops for stuff” service
This common practice consisted of receiving high-value products purchased online by criminals and reselling them on the black market by relying on residents (willingly or unwillingly) in those regions under embargo because they were associated with credit card fraud (Eastern Europe, North Africa, and Russia). The SWAT systems breach a criminal service laundering expensive goods purchased with stolen credit cards exposed its operations, structure, and earnings. This provided information on operations, finances and organizational structure, revealing the modus operandi of the redemption scams and the financial strength of the criminals involved.
The service employed more than 1,200 people in the United States who, knowingly or unknowingly, participated in drop-off scams. The structure of this service, also known as “Drops for Stuff,” distinguished “drops,” people who responded to job ads from home to drop off packages, from “stuffers,” individuals in possession of stolen credit card numbers who paid a fee for drop-off to the Swat service.
As Brian Krebs explained, most redelivery scams promised drops a monthly stipend with possible bonuses that were never actually received. In practice, packages arrived with prepaid shipping labels with stolen credit cards. The drops were responsible for inspecting and verifying the contents of the shipments, putting the correct shipping label on each package, and sending it through the appropriate shipping company. Once the stolen parcels were received and successfully returned, the traffickers could proceed to sell them on the local black market, dropping them.
“It’s not hard to see how reshipping can be a profitable venture for card fraudsters,” Krebs explains. “For example, a stuffer buys a stolen payment card on the black market for $10 and uses it to purchase over $1,100 worth of goods. After the reshipping service has taken its cut (about $550) and the stuffer has paid its reshipping label (about $100), the stuffer receives the stolen goods and sells them on the black market in Russia for $1,400. He just turned a $10 investment into more than $700.”
What to do to avoid running into these scams
It is critical to be careful when exploring offers that promise easy earnings. Offers that do not provide clear details about products, earning patterns, or company structure may hide pitfalls. Victims of these scams not only lose money, but can also be charged with receiving stolen goods or aiding and abetting criminal activity. To avoid problems, beware of job offers that are too tempting or require you to make money transfers, check the legitimacy of companies that offer abnormal redelivery opportunities.
About the author: Salvatore Lombardo (Twitter @Slvlombardo)
Electronics engineer and Clusit member, for some time now, espousing the principle of conscious education, he has been writing for several online magazine on information security. He is also the author of the book “La Gestione della Cyber Security nella Pubblica Amministrazione”. “Education improves awareness” is his slogan.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, money laudering)


Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
International Press – Newsletter
Cybercrime
BlackBerry Cylance Data Offered for Sale on Dark Web
City of Cleveland Scrambling to Restore Systems Following Cyberattack
Malware
Ransomware Attackers May Have Used Privilege Escalation Vulnerability as Zero-day
Operation Celestial Force employs mobile and desktop malware to target Indian entities
Dissecting SSLoad Malware: A Comprehensive Technical Analysis
DISGOMOJI Malware Used to Target Indian Government
Arid Viper poisons Android apps with AridSpy
Hacking
Bypassing Veeam Authentication CVE-2024-29849
Updates for security issue affecting IntelliJ-based IDEs 2023.1+ and JetBrains GitHub Plugin
Challenges in red teaming AI systems
The mystery of an alleged data broker’s data breach
GPT-4 autonomously hacks zero-day security flaws with 53% success rate
EmailGPT Exposed to Prompt Injection Attacks
Intelligence and Information Warfare
Howling at the Inbox: Sticky Werewolf’s Latest Malicious Aviation Attacks
Two Ukrainians suspected of helping Russia spread propaganda, hack military phones
Insights on Cyber Threats Targeting Users and Enterprises in Brazil
Cybersecurity
Security Alert: CVE-2024-4577 – PHP CGI Argument Injection Vulnerability
What Snowflake isn’t saying about its customer data breaches
Why are hospitals becoming more of a target for ransomware attacks
Arm Warns of Actively Exploited Zero-Day Vulnerability in Mali GPU Drivers
THE JUNE 2024 SECURITY UPDATE REVIEW
Update on cyber incident: Clinical impact in south east London – Friday 14 June 2024
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, newsletter)
ASUS addresses a critical remote authentication bypass vulnerability, tracked as CVE-2024-3080 (CVSS v3.1 score: 9.8), impacting seven router models.
The flaw is an authentication bypass issue that a remote attacker can exploit to log into the device without authentication.
The flaw impacts the following models:
The company released the following firmware update to address the issue:
The vendor also addressed a critical upload arbitrary firmware flaw, tracked as CVE-2024-3912 (CVSS score 9.8) impacting multiple devices. An unauthenticated, remote attacker can exploit the flaw to execute system commands on the vulnerable device.
Carlos Köpke from PLASMALABS discovered the flaw. Impacted products are: DSL-N17U, DSL-N55U_C1, DSL-N55U_D1, DSL-N66U, DSL-N14U, DSL-N14U_B1, DSL-N12U_C1, DSL-N12U_D1, DSL-N16, DSL-AC51, DSL-AC750, DSL-AC52U, DSL- AC55U, DSL-AC56U.
Some impacted models will not receive the firmware updates because they have reached the end-of-life (EoL).
The following versions address the flaw:
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, routers)

A 22-year-old man from the United Kingdom arrested this week in Spain is allegedly the ringleader of Scattered Spider, a cybercrime group suspected of hacking into Twilio, LastPass, DoorDash, Mailchimp, and nearly 130 other organizations over the past two years.
The Spanish daily Murcia Today reports the suspect was wanted by the FBI and arrested in Palma de Mallorca as he tried to board a flight to Italy.

A still frame from a video released by the Spanish national police shows Tylerb in custody at the airport.
“He stands accused of hacking into corporate accounts and stealing critical information, which allegedly enabled the group to access multi-million-dollar funds,” Murcia Today wrote. “According to Palma police, at one point he controlled Bitcoins worth $27 million.”
The cybercrime-focused Twitter/X account vx-underground said the U.K. man arrested was a SIM-swapper who went by the alias “Tyler.” In a SIM-swapping attack, crooks transfer the target’s phone number to a device they control and intercept any text messages or phone calls sent to the victim — including one-time passcodes for authentication, or password reset links sent via SMS.
“He is a known SIM-swapper and is allegedly involved with the infamous Scattered Spider group,” vx-underground wrote on June 15, referring to a prolific gang implicated in costly data ransom attacks at MGM and Caesars casinos in Las Vegas last year.
Sources familiar with the investigation told KrebsOnSecurity the accused is a 22-year-old from Dundee, Scotland named Tyler Buchanan, also allegedly known as “tylerb” on Telegram chat channels centered around SIM-swapping.
In January 2024, U.S. authorities arrested another alleged Scattered Spider member — 19-year-old Noah Michael Urban of Palm Coast, Fla. — and charged him with stealing at least $800,000 from five victims between August 2022 and March 2023. Urban allegedly went by the nicknames “Sosa” and “King Bob,” and is believed to be part of the same crew that hacked Twilio and a slew of other companies in 2022.
Investigators say Scattered Spider members are part of a more diffuse cybercriminal community online known as “The Com,” wherein hackers from different cliques boast loudly about high-profile cyber thefts that almost invariably begin with social engineering — tricking people over the phone, email or SMS into giving away credentials that allow remote access to corporate internal networks.
One of the more popular SIM-swapping channels on Telegram maintains a frequently updated leaderboard of the most accomplished SIM-swappers, indexed by their supposed conquests in stealing cryptocurrency. That leaderboard currently lists Sosa as #24 (out of 100), and Tylerb at #65.
In August 2022, KrebsOnSecurity wrote about peering inside the data harvested in a months-long cybercrime campaign by Scattered Spider involving countless SMS-based phishing attacks against employees at major corporations. The security firm Group-IB called the gang by a different name — 0ktapus, a nod to how the criminal group phished employees for credentials.
The missives asked users to click a link and log in at a phishing page that mimicked their employer’s Okta authentication page. Those who submitted credentials were then prompted to provide the one-time password needed for multi-factor authentication.
These phishing attacks used newly-registered domains that often included the name of the targeted company, and sent text messages urging employees to click on links to these domains to view information about a pending change in their work schedule. The phishing sites also featured a hidden Telegram instant message bot to forward any submitted credentials in real-time, allowing the attackers to use the phished username, password and one-time code to log in as that employee at the real employer website.
One of Scattered Spider’s first big victims in its 2022 SMS phishing spree was Twilio, a company that provides services for making and receiving text messages and phone calls. The group then pivoted, using their access to Twilio to attack at least 163 of its customers.
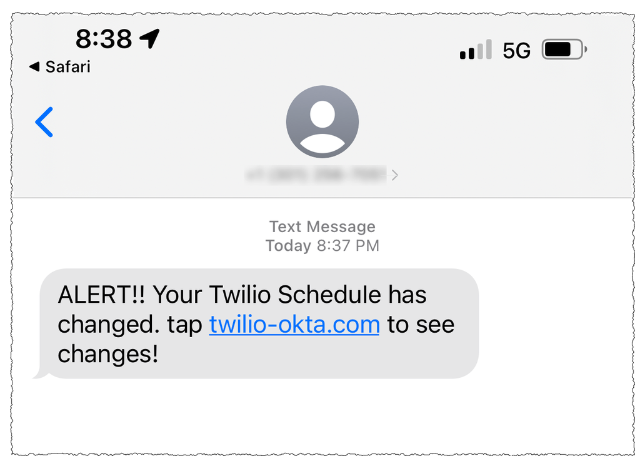
A Scattered Spider phishing lure sent to Twilio employees.
Among those was the encrypted messaging app Signal, which said the breach could have let attackers re-register the phone number on another device for about 1,900 users.
Also in August 2022, several employees at email delivery firm Mailchimp provided their remote access credentials to this phishing group. According to Mailchimp, the attackers used their access to Mailchimp employee accounts to steal data from 214 customers involved in cryptocurrency and finance.
On August 25, 2022, the password manager service LastPass disclosed a breach in which attackers stole some source code and proprietary LastPass technical information, and weeks later LastPass said an investigation revealed no customer data or password vaults were accessed.
However, on November 30, 2022 LastPass disclosed a far more serious breach that the company said leveraged data stolen in the August breach. LastPass said criminal hackers had stolen encrypted copies of some password vaults, as well as other personal information.
In February 2023, LastPass disclosed that the intrusion involved a highly complex, targeted attack against an engineer who was one of only four LastPass employees with access to the corporate vault. In that incident, the attackers exploited a security vulnerability in a Plex media server that the employee was running on his home network, and succeeded in installing malicious software that stole passwords and other authentication credentials. The vulnerability exploited by the intruders was patched back in 2020, but the employee never updated his Plex software.
Plex announced its own data breach one day before LastPass disclosed its initial August intrusion. On August 24, 2022, Plex’s security team urged users to reset their passwords, saying an intruder had accessed customer emails, usernames and encrypted passwords.
Sosa and Tylerb were both subjected to physical attacks from rival SIM-swapping gangs. These communities have been known to settle scores by turning to so-called “violence-as-a-service” offerings on cybercrime channels, wherein people can be hired to perform a variety geographically-specific “in real life” jobs, such as bricking windows, slashing car tires, or even home invasions.
In 2022, a video surfaced on a popular cybercrime channel purporting to show attackers hurling a brick through a window at an address that matches the spacious and upscale home of Urban’s parents in Sanford, Fl.
January’s story on Sosa noted that a junior member of his crew named “Foreshadow” was kidnapped, beaten and held for ransom in September 2022. Foreshadow’s captors held guns to his bloodied head while forcing him to record a video message pleading with his crew to fork over a $200,000 ransom in exchange for his life (Foreshadow escaped further harm in that incident).
According to several SIM-swapping channels on Telegram where Tylerb was known to frequent, rival SIM-swappers hired thugs to invade his home in February 2023. Those accounts state that the intruders assaulted Tylerb’s mother in the home invasion, and that they threatened to burn him with a blowtorch if he didn’t give up the keys to his cryptocurrency wallets. Tylerb was reputed to have fled the United Kingdom after that assault.
KrebsOnSecurity sought comment from Mr. Buchanan, and will update this story in the event he responds.
NHS England confirmed that the recent ransomware attack on Synnovis had a severe impact of multiple London hospitals, forcing them to cancel more than hundreds of scheduled operations.
Synnovis is a pathology partnership between Guy’s and St Thomas’ NHS Foundation Trust and King’s College Hospitals NHS Trust, and SYNLAB, Europe’s largest provider of medical testing and diagnostics.
In a post published on its website, Synnovis disclosed it was the victim of a ransomware attack.
The pathology and diagnostic services provider has launched an investigation into the security breach with the help of experts from the NHS. The experts are working to fully assess the impact of the attack and to take the appropriate action to contain the incident. The company also announced they are working closely with NHS Trust partners to minimise the impact on patients and other service users.
Law enforcement suspects that Qilin extortion group is behind the attack. The NHS London published a statement on Synnovis ransomware attack confirming that the incident is having a significant impact on the delivery of services at Guy’s and St Thomas’, King’s College Hospital NHS Foundation Trusts and primary care services in south east London.
“On Monday 3 June Synnovis, a provider of lab services, was the victim of a ransomware cyber attack. This is having a significant impact on the delivery of services at Guy’s and St Thomas’, King’s College Hospital NHS Foundation Trusts and primary care services in south east London and we apologise for the inconvenience this is causing to patients and their families.” reads the statement published by NHS London.
“All urgent and emergency services remain open as usual and the majority of outpatient services continue to operate as normal.” continues the NHS. “Unfortunately, some operations and procedures which rely more heavily on pathology services have been postponed, and blood testing is being prioritised for the most urgent cases, meaning some patients have had phlebotomy appointments cancelled.”
On Friday 14, June, NHS London confirmed that King’s College Hospital NHS Foundation Trust and Guy’s and St Thomas’ NHS Foundation Trust canceled more than 800 planned operations and 700 outpatient appointments. According to the statement from NHS London, the majority of planned activity were not interrupted, but the incident specifically impacted some specialities more than others.
“The data for the first week after the attack (3-9 June) shows that, across the two most affected Trusts – King’s College Hospital NHS Foundation Trust and Guy’s and St Thomas’ NHS Foundation Trust – more than 800 planned operations and 700 outpatient appointments needed to be rearranged. The majority of planned activity has continued to go ahead, with some specialities impacted more than others.” reads statement from the NHS England. “Trusts are working hard to make sure any procedures are rearranged as quickly as possible, including by adding extra weekend clinics.”
Synnovis is working on recovering impacted systems, planning to restore some functionality in the coming weeks. Full restoration will take longer, and the need to reschedule tests and appointments will cause ongoing disruptions over the next few months.
Early this week, the UK National Health Service (NHS) issued an urgent call for O-type blood donations due to the recent ransomware attack on Synnovis that disrupted operations at several healthcare organizations in London.
The NHS confirmed that the ransomware attack has disrupted blood matching tests, for this reason, affected hospitals are using O Negative and O Positive blood for patients who can’t wait for alternative matching methods. For this reason, the NHS is calling for O-type blood donations.
“England’s top doctor has today (Monday 10 June) backed calls from NHS Blood and Transplant (NHSBT) for O Positive and O Negative blood donors to urgently book appointments to donate in one of the 25 town and city centre NHS Blood Donor Centres in England, to boost stocks of O type blood following the cyber incident in London.” reads the announcement published by the NHS Blood and Transplant.
“The IT incident affecting a pathology provider means the affected hospitals cannot currently match patients’ blood at the same frequency as usual. For surgeries and procedures requiring blood to take place, hospitals need to use O type blood as this is safe to use for all patients and blood has a shelf life of 35 days, so stocks need to be continually replenished. That means more units of these types of blood than usual will be required over the coming weeks to support the wider efforts of frontline staff to keep services running safely for local patients.”
O Negative blood is a universal blood type, anyone can receive it, for this reason, it is crucial in emergencies or when a patient’s blood type is unknown. Despite only 8% of the population having O Negative, it accounts for about 15% of hospital orders. O Positive, the most common blood type, can be given to anyone with a positive blood type, benefiting 76% of the population. 35% of blood donors have O Positive blood.
“To support London hospitals to carry out more surgeries and to provide the best care we can for all patients, we need more O Negative and O Positive donors than usual. Please book an urgent appointment to give blood at one of our 25 town and city donor centres which currently have good appointment availability.” said Dr Gail Miflin, Chief Medical Officer, NHS Blood and Transplant. “We have availability for donors who know they are type O but we also welcome new donors who don’t yet know their blood type. You might have one of these special types that can be used in emergencies.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, London hospitals)



In January 2025, financial and insurance institutions in Europe and any organizations that do business with them must comply with the Digital Operation Resilience Act, also known as DORA. This regulation from the European Union (EU) is intended to both strengthen IT security and enhance the digital resilience of the European financial market. Much like GDPR, this act promises to exert significant influence on the activities of organizations around the world. Its official launch date of January 17, 2025, means there are some pretty stringent deadlines.
Can this be done? Will organizations be ready? These were questions posed in a recent podcast with guest Romain Deslorieux, Strategic Partners Director, Global System Integrators at Thales. He suggested that it might be a “tough call for any organization to follow and to reach as a compliance deadline.” But he also pointed out that the European Supervisory Authority (ESA) is busy defining some of the regulatory technical standards that will provide precise and technical guidelines for organizations to follow. He added that most financial entities have already started to investigate DORA, including defining a roadmap, although it may be time for them to accelerate these activities.
Companies that operate in the world of finance and insurance are no strangers to broad regulations, both internal and international. Still, DORA is a reminder of just how agile they must remain, given that speed is all around them. The incredible rate at which AI technologies were discovered and embraced by end users and then deployed into workplaces everywhere shows just how difficult it can be for an organization to keep on a safe and even keel. The challenge doubles when we factor in the relentless creativity and determination of a criminal element that is always keen to exploit new technologies before adequate safeguards are implemented.
Perhaps one of the most striking elements of DORA is its focus on third-party risk management, which is one of its key pillars. Additional podcast guest Mark Hughes, Global Managing Partner, Cybersecurity Services, IBM Consulting, pointed out how events such as Colonial Pipeline clearly showed how a single piece of a supply chain can have a disproportionate impact on all the other parts. He says this is why DORA places such focus on third-party risk management – not just in conducting risk assessments but also monitoring them.
In a single word, the DORA initiative is about resilience. That’s what the “R” stands for, after all. It’s an updated effort to enhance a fortress while still allowing the free movement of the vital data that keeps economies going.
Sticking with the supply chain in the context of resilience, Romain suggests we take a lesson from cloud technology. Cloud systems and services, he says, represent an essential part of operational resilience, and being a central point of an organization’s data, they must remain up and available. Yet, at the same time, they are also subject to challenges of territoriality in terms of where data can be stored, where the most influential cloud organizations come from, and how sovereignty can be maintained.
The fact is there’s not much time for companies to get their various ducks in a row. Therefore, financial organizations based in Europe that will be at the forefront of compliance preparation must fully assess their current digital systems and processes to find vulnerabilities and resilience gaps. They must also strengthen cybersecurity measures, including encryption, firewalls, and regular security audits, and have incident response plans in place. The same type of requirements should be made for operational risk management and business continuity planning, both of which help ensure they can maintain critical operations in the event of disruptions or cyberattacks.
Strategic activities to be built into this very short timeline include ongoing vigilance of DORA itself within an evolving regulatory landscape, increased or improved collaboration and information sharing, investment in technology and talent, and improved board oversight and governance.
Organizations based outside the areas where DORA directly applies (most of Europe plus Iceland and Norway), should also ensure they understand DORA Requirements and open communication channels with their European partners. In addition to staying informed, they may also consider adopting other internationally recognized cybersecurity and operational resilience standards and frameworks, such as ISO 27001 for information security management and ISO 22301 for business continuity management.
It is virtually guaranteed that similar sets of regulations will be imposed by other economic areas of the world, creating challenges for companies either in finance or working with them. This promises to generate sets of economic blocks at the same time as it opens new areas of commerce. However, these changes are best seen as opportunities to finetune an organization’s information security systems and to reaffirm relationships with vendors and experts to ensure continued security and compliance.
About the author: Steve Prentice
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Europe financial industry)

